Hello flatboard community,
I am going to be working on a new security plugin called FlatSecurity. If anyone has a better name please tell me, I'm terriable with project names
What is this
This is a flatboards personal risk management addon that will detect any software that might be a risk to this software or your device.
@Fred please don't make this because I want to make it.
Objectives
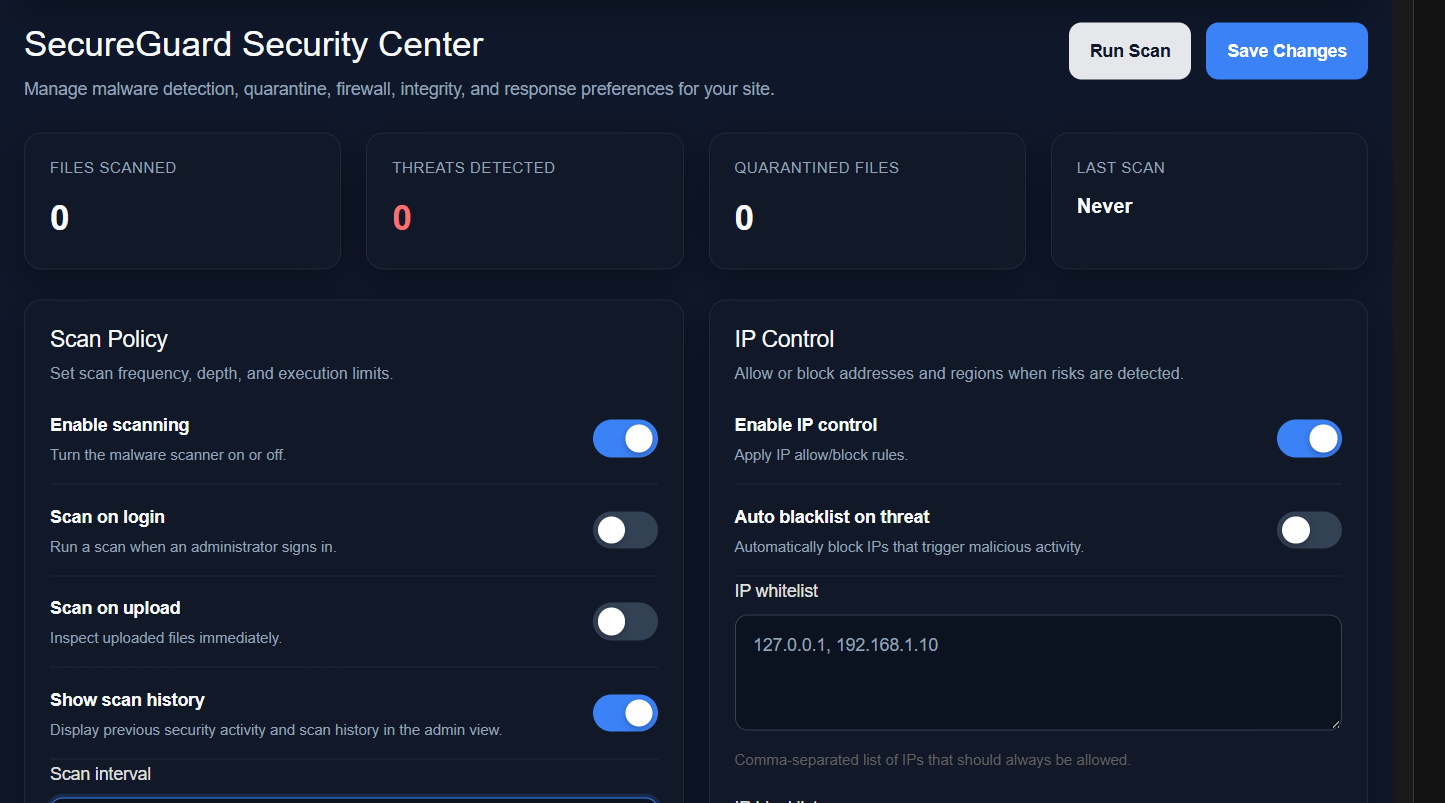
- Manual/Auto detect security risk codes
- Displays the risk and how to improve it
- Has a leveling system of the risk (customizable ranking)
low,medium,high, andsevere - It would use the CVE guidelines and CWE guidelines and label the information security risks
- Security history will always be stored. (This CANNOT be deleted)
Configurations
- Customizable secuirty rankings
- Scheduled automation (
hourly,daily,weekly,monthly, andyearly) - Select file/folder to get a quick check any vulnerabilities
- Actions:
- Quick Scan (Scans a specific directory)
- Quarantine (Quarantines a file or directory)
- Remove (Removes a file or directory)
- Resolve options
- False positive - Alert has found a false positive
- Used in test - Ignore the directory/file because it was used for testing purposes
- Won't fix - Means you fixed the issue but still reads it.
- Description: A short description of closure
Adminsitrator side
- Security history outline of past security risks that may have been found. This is to prevent future problems
- Number of security risk in the past
1h,24h,1w,1m,1y - A graph showing the risks and threats
- It will show the number of each malware i.e.
virus,adware,ransomware,spyware,rootkits,keyloggers,bots,Fileless malware,cryptojacking, andwiper attacks - View quarantine/removed files
APIs
FlatSecurity::quickScan(string|string[] $FileOrDir): SecurityReport- Does a quick scan for any list of vulnerabilies in a directory(ies)/file(s).FlatSecurity::quarantine(string|string[] $FileOrDir): bool- Quarantines any file(s)/directory(ies) and returns a boolean if its successfully did the task.FlatSecurity::remove(string|string $FileOrDir): bool- Removes any file(s)/directory(ies) the the deviceFlatSecurity::setSchedule(int $time, string $duration): void- Sets the automation schedule time.time: number of durations anddurationis the short version of the time i.e. s=>seconds; i=>minutes; h=>hours; d=>days; m=>month; y=>yearsFlatSecurity::scanUpload(string $name, string|array $settings='balanced'): SecurityReport- Scans everything from the uploaded file. You can customize your settings
| | Lazy | Balanced | Strict |
|---------------------|----------------------------------------------------------------------|-----------------------------------------------|--------------------|
| File types | Documents, Images, Audio/Video, Archives, Code/Scripts, Executables | Documents, Images, Audio/Video, Archives | Documents, Images |
| Max file size | 250 MB | 25 MB | 5 MB |
| MIME + magic bytes | ⚠️ Partial | ✅ Required | ✅ Required |
| AV scanning | ❌ No support | ✅ Supported | ✅ Supported |
| Content sanitization| ❌ No support | ✅ Supported | ✅ Supported |
| Storage isolation | ✅ Supported | ✅ Supported | ✅ Supported |
| Execution disabled | ✅ Supported | ✅ Supported | ✅ Supported |
| Logging & alerts | ⚠️ Partial | ✅ Supported | ✅ Supported |
| File naming | Original name | Sanitized | Randomized UUID |
| Multiple files per request | ✅ allowed | ⚠️ Allowed with limit | ❌ Disabled |
| Error handling | Silent / generic | User‑friendly | Logged + generic |
| CSRF protection | ❌ No support | ⚠️ Enabled | ✅ Required |
PHP array (if used for custom)
$config = [
'types'=>'...', # file extenstions (without the ".")
'size'=>5000000, # in Bytes
'mmb'=>true, # MIME + magic bytes TRUE/FALSE
'avscanning'=>true, # AV Scanning TRUE/FALSE
'sanitization'=>true, # Content sanitization
'isolation'=>false, # Storage isolation
'execution'=>false, # Execution
'logging'=>false, # Logging
'alerts'=>false, # Alerts
'naming'=>'original', # File nameing 'original', 'sanitize', 'random'
'multiple'=>false, # Multiple files
'error'=>'silent', # 'silent', 'friendly', 'logged'
'crsf'=>true, # CSRF protection
]
FlatSecurity::ScanCompression(string $zip):SecurityReport- Scans through any compression files i.e. zip, 7Z, RAR, etc.FlatSecurity::getMalwareType(string $codeline): string- Detects the kind of malware base on the type of codeFlatSecurity::getCVE(SecurityReport $report): string- Returns the CVE guidline issueFlatSecurity::getCWE(SecurityReport $report): string- Returns the CVE guidline issueFlatSecurity::isXSS(string $code): bool- Returns a boolean if there is a XSSFlatSecurity::isSQLInjection(string $code): bool- Returns a boolean if there is a SQL InjectionFlatSecurity::isVirus(string $file): bool- Returns a boolean if the file is a virusFlatSecurity::isAdware(string $file): bool- Returns a boolean if the file is a adwareFlatSecurity::iRansomware(string $file): bool- Returns a boolean if the file is a RansomwareFlatSecurity::isSpyware(string $file): bool- Returns a boolean if the file is a spywareFlatSecurity::isRootkit(string $file): bool- Returns a boolean if the file is a rootkitFlatSecurity::isKeyLogger(string $file): bool- Returns a boolean if the file is a keyloggerFlatSecurity::isBot(string $file): bool- Returns a boolean if the file is a botFlatSecurity::isFileless(string $file): bool- Returns a boolean if the file is a Fileless MalwareFlatSecurity::isCryptojacking(string $file): bool- Returns a boolean if the file is a cryptojackingFlatSecurity::isWiper(string $file): bool- Returns a boolean if the file is a wiper attack
More will be added on future includements
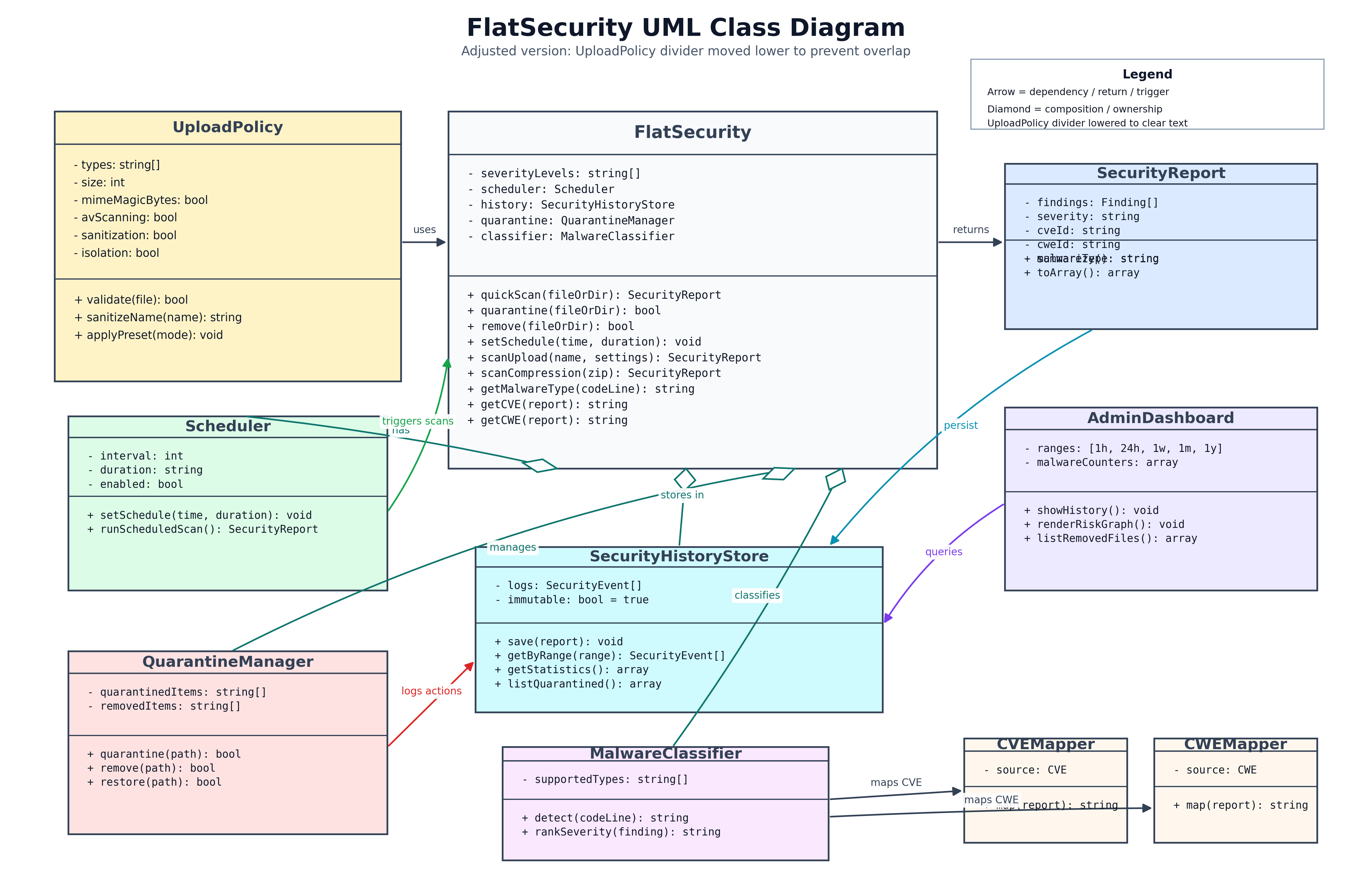
Diagram
Note: This is a AI generated diagram, so it may not be up-to-scale
Edited on Mar 26, 2026 By Gavin .